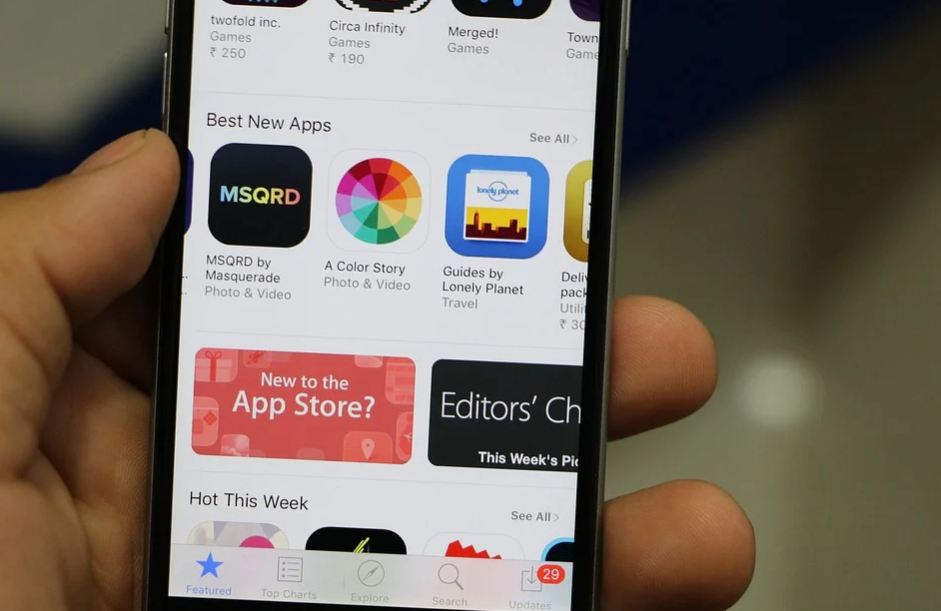
Although it is relatively unlikely to envision life without owning smartphones as they have changed our lives nowadays, a smartphone’s functionality always depends on many different things. In this case, there are two vital factors, such as some apps installed on your device and the number of apps that you can download on that device. Generally, iPhone users can download apps through App Stores or websites that offer IPA versions of several apps. However, one main disadvantage of using the App Store is that they rely little on the operating systems to do their job.
 Fortunately, there are third-party app stores that anyone can use. Some may work with almost all platforms, but some apps are best working on iPhone. Such a third-party app has an excellent user interface and experience. The users can navigate the apps well, and it does not require additional apps and supporting multiple languages. Therefore, this article wants to share some third-party apps that work best for iOS devices below. This way, iPhone users can find and get programs and other files in a comfortable way.
Fortunately, there are third-party app stores that anyone can use. Some may work with almost all platforms, but some apps are best working on iPhone. Such a third-party app has an excellent user interface and experience. The users can navigate the apps well, and it does not require additional apps and supporting multiple languages. Therefore, this article wants to share some third-party apps that work best for iOS devices below. This way, iPhone users can find and get programs and other files in a comfortable way.
AppCake
AppCake might be one of the best third-party apps for iPhone users. Many have left a positive review for its best app collection. You can search or browse games and apps by categories, and the interface is easy to understand and comprehend. Also, AppCake offers the option of downloading paid apps and games until you can use them. This way, you can benefit from the features without spending a dime.
might be one of the best third-party apps for iPhone users. Many have left a positive review for its best app collection. You can search or browse games and apps by categories, and the interface is easy to understand and comprehend. Also, AppCake offers the option of downloading paid apps and games until you can use them. This way, you can benefit from the features without spending a dime.
AppValley
iOS users would be happy to have AppValley on their device, either iPhone, iPad, or Mac. Its easy-to-use interface allows users to get a massive selection of games and programs for their mobile devices in a couple of seconds. AppValley is not only a superb alternative but also an excellent replacement for Apple’s official App Store.
Apps4iPhone
As mentioned in its name, this app offers exclusive service for iPhone, iPad, and Mac users. With the Apps4iPhone, users can download games and apps on their devices for free and fast. Its interface is also excellent, so you won’t feel confused or frustrated when looking for the app you want.
Aptoide
 According to how it works, Aptoide is one of many excellent third-party apps. However, Aptoide includes many things that you might not discover on some third-party apps mentioned above. They give more than just downloading apps and games to mobile units quickly and free of charge. Aptoide allows developers to submit their programs to this third-party app store. In other words, you can see programs or perhaps games on Aptoide that you can’t see elsewhere.
According to how it works, Aptoide is one of many excellent third-party apps. However, Aptoide includes many things that you might not discover on some third-party apps mentioned above. They give more than just downloading apps and games to mobile units quickly and free of charge. Aptoide allows developers to submit their programs to this third-party app store. In other words, you can see programs or perhaps games on Aptoide that you can’t see elsewhere.
Third-party app stores offer several benefits to iOS users. One of them is by downloading apps for free and accessible. However, it would be best to stay very cautious before testing the waters and applying such third-party app stores.





 Tablets provide a great way to access apps and other online resources on the go. They offer portability, high performance, and long battery life to do more in less time. Plus, many models have a built-in keyboard, meaning you don’t have to carry around an extra laptop or netbook.
Tablets provide a great way to access apps and other online resources on the go. They offer portability, high performance, and long battery life to do more in less time. Plus, many models have a built-in keyboard, meaning you don’t have to carry around an extra laptop or netbook.


