Mobile apps have become a vital part of our daily lives in today’s digital age. From ordering food to booking a taxi, we rely on these apps for various purposes. However, your app must stand out with millions of apps available on the app stores. This is where mobile app development comes into play: crafting an application that looks visually appealing, performs efficiently, and provides a great user experience. On the other hand, if you want to build apps without code, keep on reading. In this blog post, we will discuss some crucial aspects of mobile app development that can make or break your app’s success in the market.
User Experience

User experience (UX) is one of the most important aspects of mobile app development. It refers to how users interact with your app, including its design, usability, and functionality. A well-designed UX ensures that users can easily navigate through your app’s features without experiencing any glitches or frustration. To create a great user experience, you need to understand your target audience and their needs. You can identify pain points and design solutions by conducting research and analyzing user behavior patterns. This includes creating an intuitive user interface (UI), ensuring fast loading times, providing clear instructions on how to use the app’s features, and designing simple but effective navigation menus.
Security
Mobile app development is an exciting process, but it also comes with its own set of challenges. Security is a major aspect that developers must keep in mind during the development process. With the increasing number of cyber threats and data breaches, ensuring your mobile app is secure has become more important than ever. The first step towards securing your mobile app is to use strong encryption techniques to protect sensitive information from being accessed by unauthorized users. This includes encrypting user data such as login credentials, financial transactions, and other personal information. Another important aspect of security in mobile apps is implementing proper authentication measures to prevent unauthorized access. This can be achieved through two-factor authentication or biometric authentication like fingerprint scanning or facial recognition.
Easy Navigation
 Easy Navigation is a crucial aspect of mobile app development as it enhances user experience. A well-designed navigation system can help users easily find what they are looking for, making their interaction with the app seamless and effortless. To ensure easy navigation, developers need to consider various factors, such as the placement of menus, buttons, and icons. It’s important to avoid cluttering the interface with too many options that may confuse or overwhelm users. Instead, developers should aim for simplicity while providing all necessary features. Another key consideration for easy navigation is consistency. Users should be able to navigate through different sections of the app without relearning how to use it every time they open a new page or feature.
Easy Navigation is a crucial aspect of mobile app development as it enhances user experience. A well-designed navigation system can help users easily find what they are looking for, making their interaction with the app seamless and effortless. To ensure easy navigation, developers need to consider various factors, such as the placement of menus, buttons, and icons. It’s important to avoid cluttering the interface with too many options that may confuse or overwhelm users. Instead, developers should aim for simplicity while providing all necessary features. Another key consideration for easy navigation is consistency. Users should be able to navigate through different sections of the app without relearning how to use it every time they open a new page or feature.
To sum up, mobile app development is a complex process that requires attention to detail and focus on several aspects. User experience is the most important of all, followed by security and easy navigation. A well-designed app can make or break a business and its reputation in the market. So if you are planning to develop your own app or hire a professional team of developers for it, ensure that these crucial aspects are given due consideration during every stage of development. Remember, creating an efficient and successful mobile application requires more than just coding skills – it needs creativity, insightfulness, and an understanding of user expectations.





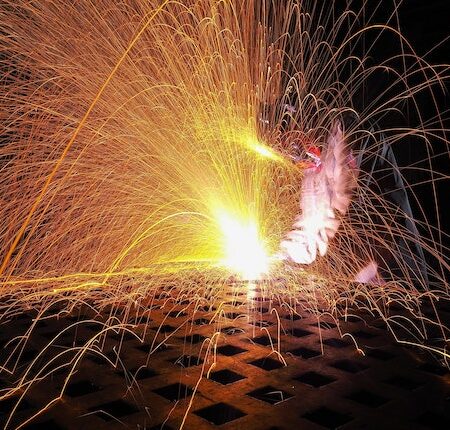
 Another option for oxide layer removal is mechanical removal. This involves using abrasive materials, such as sandpaper or steel wool, to physically scour the oxides off the surface. It can be effective but requires much manual labor and patience to achieve a smooth finish. It also has the potential to leave unwanted scratches on the surface. In addition, due to the high temperatures involved in laser cutting, there is a risk of burning off too much material, potentially weakening the structure. Also, there is a greater risk of generating hazardous dust particles, so personal protective equipment such as masks and eye protection is recommended.
Another option for oxide layer removal is mechanical removal. This involves using abrasive materials, such as sandpaper or steel wool, to physically scour the oxides off the surface. It can be effective but requires much manual labor and patience to achieve a smooth finish. It also has the potential to leave unwanted scratches on the surface. In addition, due to the high temperatures involved in laser cutting, there is a risk of burning off too much material, potentially weakening the structure. Also, there is a greater risk of generating hazardous dust particles, so personal protective equipment such as masks and eye protection is recommended. The third method for removing oxide layers from laser-cut surfaces is thermal removal. This technique uses a torch or furnace to heat and evaporates the surface oxides. This can be useful for thick layers of oxides, as it is much faster than the other two methods. However, it should be done cautiously as temperatures above 1,100°F (593°C) can damage or even warp the material. Additionally, this method requires specialized equipment and expertise to perform safely. When done correctly, thermal removal can achieve a smooth finish with minimal heat damage.
The third method for removing oxide layers from laser-cut surfaces is thermal removal. This technique uses a torch or furnace to heat and evaporates the surface oxides. This can be useful for thick layers of oxides, as it is much faster than the other two methods. However, it should be done cautiously as temperatures above 1,100°F (593°C) can damage or even warp the material. Additionally, this method requires specialized equipment and expertise to perform safely. When done correctly, thermal removal can achieve a smooth finish with minimal heat damage.

